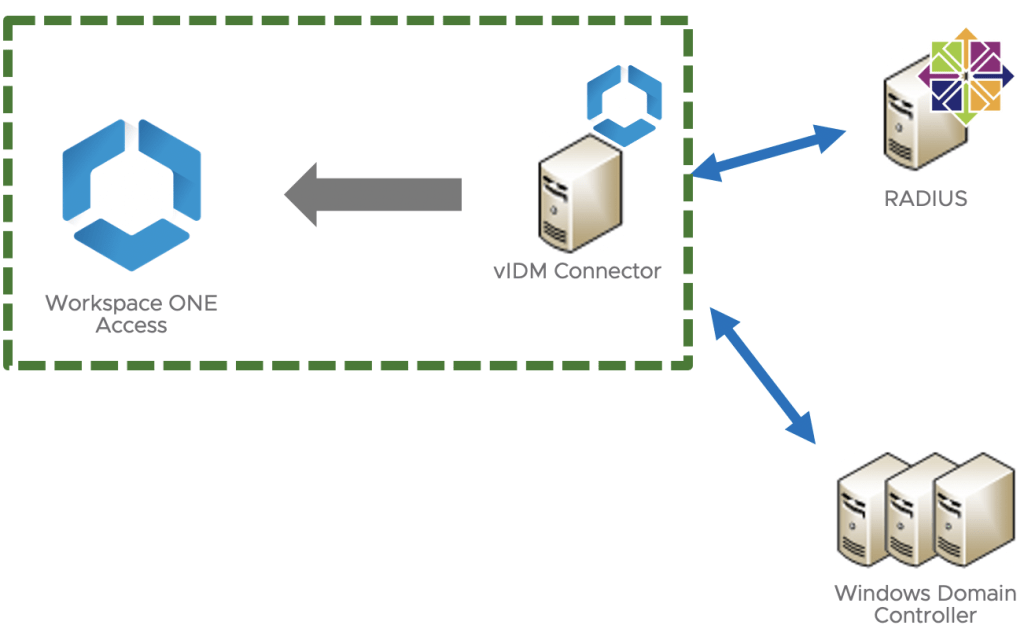
If you follow the steps from Part I, your RADIUS server is properly configured and you have Google Authenticator working as well. Now it’s time to finish our integration from Workspace ONE Access side.
Configuring Radius Authentication – Workspace ONE Access
Whether you’re using On-Premises or SaaS, all configuration steps will be basically the same, so you’ll be fine following this along.
Log into Workspace ONE Access
Note: My domain username has Super Admin role, so I’ll have all privileges required to conclude this task.

First – Configuring Radius Authentication into vIDM Connector
When you’re logged into VMware Workspace ONE Access, click on Identity & Access Management tab:

Click on Setup (right upper corner):

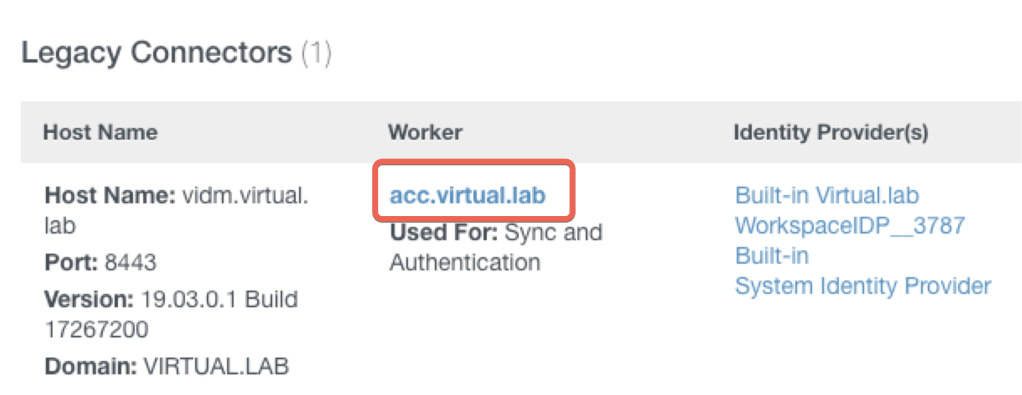
You can see your VMware Connector information in here. If you need help on how to configure your VMware Identity Manager Connector (vIDM), check this post to help you out.
Click into your vIDM Worker name (in my case, acc.virtual.lab):
Select Auth Adapters tab and right after, click on RadiusAuthAdapter:

You’ll be redirected to the Workspace ONE Access page which will be possible to configure RadiusAuthAdapter:
The following page will show with all fields to be completed based on your previous configuration (RADIUS setup):
Note: In Accounting port, I didn’t configure it because I don’t have it enabled in my environment. If you don’t have either, leave it blank. I had problems during my setup because I set a port which was not available and faced login problems. Be aware of it.

At the same Authentication Adapter page, you can configure your second RADIUS server if you have another one. As soon you’re done with this configuration hit DONE button at the bottom of the page.

All right, so now you have RadiusAuthAdapter Enabled.

Second – Configuring Radius (Cloud Deployment) using Built-In
It’s time to set Radius (Cloud Deployment) using Built-in Identity Provider.
1 – Click on Identity & Access Management
2 – Click on Identity Providers
3 – Click on Built-in

My environment is already configured so it might appear a little bit different from yours.
You’ll need to enable RADIUS (Cloud Deployment) to be used along with your Connector and your Domain. In my case, I have Password (Cloud Deployment) as well selected.

Note: If you have other Network Ranges in your environment, make sure you select the proper one for your use case. I have only one so I’ll let All Ranges enabled.

Save it afterwords.

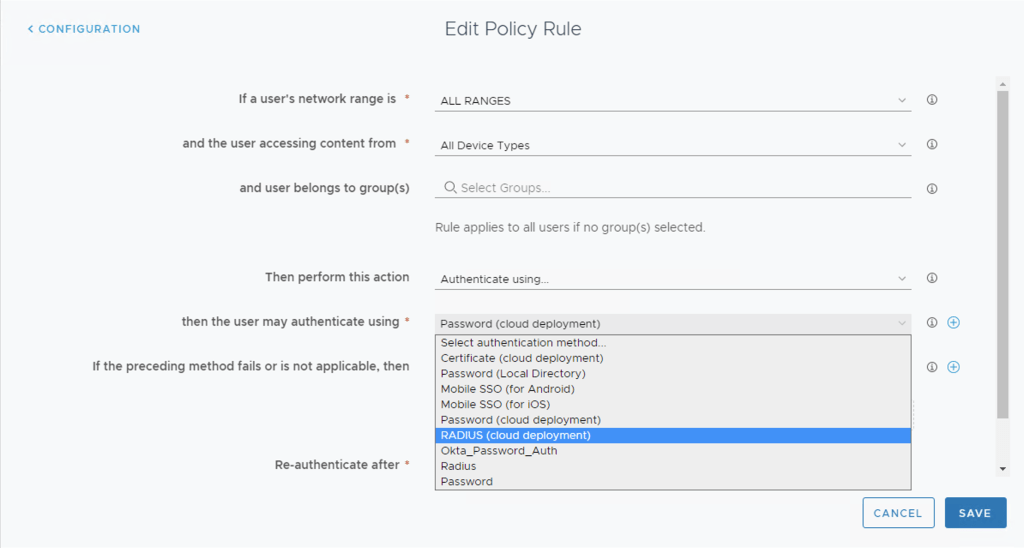
Third – Configuring Policies
The last part you need to configure in your environment will be Policies, which will required to use RADIUS (Cloud Deployment) as an authentication method.
Click on Identity & Access Management tab, click on Policies, select your Policy to be used (in my case I’m using default_access_policy_set, and edit this:

Under Configuration, select your All Ranges to be configured for RADIUS. In my case, I let this option being the first one for my use case. Select yours based on what is the best for you / your customer.

Select Radius (Cloud Deployment) to be used on this Policy.
Save it afterwords to apply this new configuration.
Testing Time
As a best alternative, open an Incognito / Private / InPrivate tab using your browser for testing. This is the recommended way to avoid cache giving you a hard time.

If all steps were configured properly, you’ll see RADUS authentication request coming from your Workspace ONE Access:
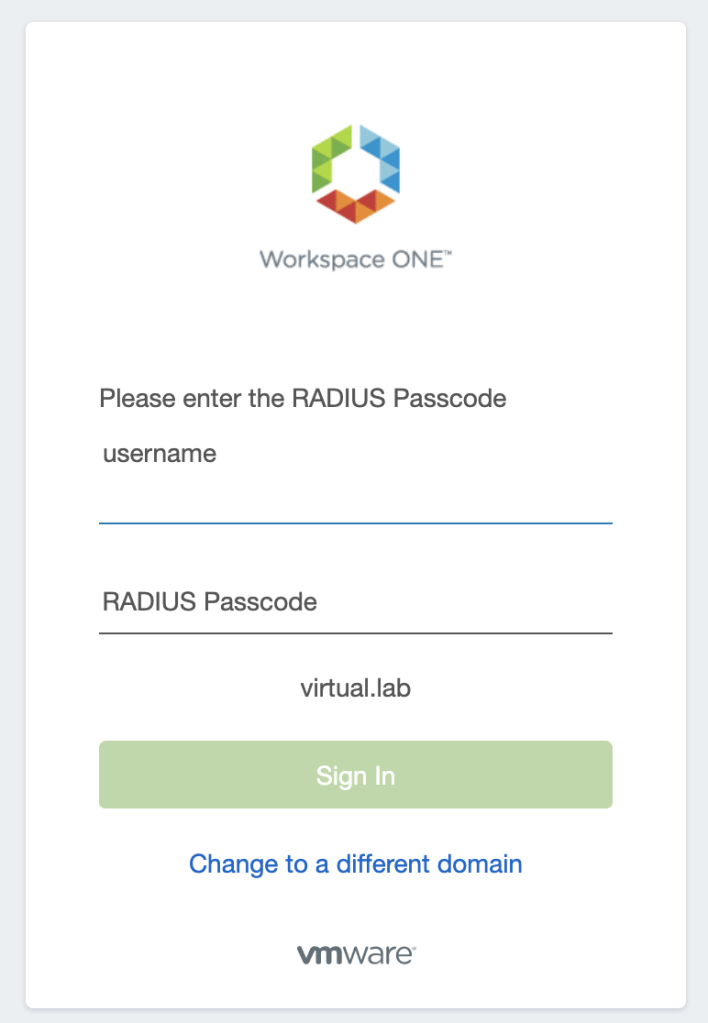
Note: Remember, RADIUS configuration was done to ask Active Directory Domain + RADIUS Passcode. So the way to type your RADIUS Passcode will be like:
RADIUS Passcode: P@ssword123456
Black = Your Active Directory Password
Red = Your Google Authenticator Passcode
Check the Video I created demonstrating how to log on.
Congratulations! If you’re here, it means you’re ready to start using VMware Workspace ONE Access along with RADIUS + Google Authenticator.
Enjoy the ride!
1 comments on “Integrating Workspace ONE Access with Google Authenticator (RADIUS) – Part II”