I was in charge in a PoC for a customer which their use case was a simple one, but took a couple of time for me to solve it based on the following error: Enrollment CertStat: NOT_VALID.
Use Case: Use TrueSSO to access an Active Directory application using RADIUS authentication.
If you’re not familiar with VMware TrueSSO and VMware Workspace One Access (formely VMware Identity Manager), I invite you to check those great blog posts from VMware:
https://blogs.vmware.com/euc/2016/03/true-sso-single-sign-on-view-identity-manager-authenticate.html
https://blogs.vmware.com/euc/2016/04/true-sso-setting-up-in-a-lab.html
During my research, I found some articles and a VMware KB showing possible ways why VMware Enrollment Server was not online.
So I start my troubleshooting:
Symptom
- Customer renewed CA Certificate in the past;
- VMware Enrollment Server was able to request Certificate using TrueSSO Template previously created;
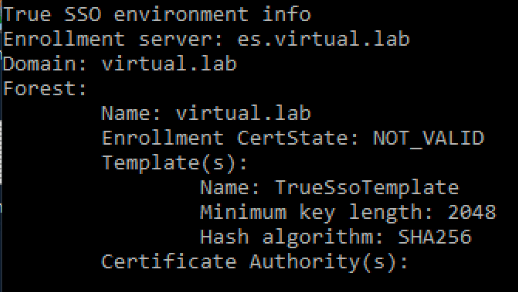
- I used the True SSO Diagnostic Utility to gain visibility and I found the following, using the command line: vdmutil –authAs poweruser –authDomain virtual –authPassword ******** –truesso –environment –list –enrollmentServer es.virtual.lab –domain virtual.lab
Solution
Those were the steps I took for correct this problem:
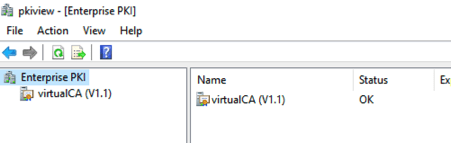
- Access pkiview.msc into customer ADCS:
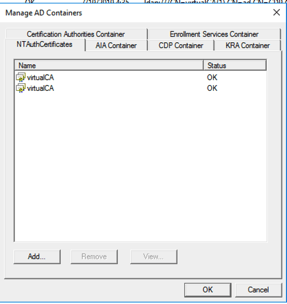
- Right click into Enterprise PKI and select Manager AD Containers;
- On NTAuthCertificates, I were able to see only one certificate (old one);

- Exported the new CA that has been created from ADCS and imported into this view:
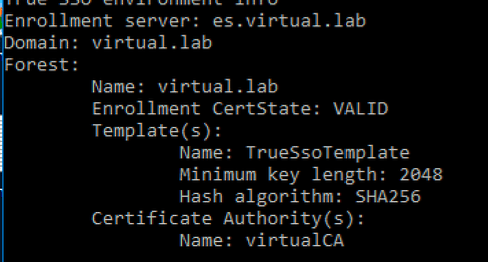
- Service has been restarted:
net stop certsvc && net start certsrv
Now customer was able to move forward into TrueSSO configuration steps:
I wish this solution can bring yours, in case you’re facing this kind of error as well.
Enjoy the ride!
For anyone who is wondering why this resolved the issue, the NTAuth store in AD is the location that defines which Certificate Authorities (CA) are authorized and trusted to issue Smartcard certificates for an enterprise. If a CA in an Active Directory environment is deployed and configured to issue Smartcard certificates, but is not added to the NTAuth store smartcard issuance will fail.
LikeLike
Thanks for you comment Charles! Great info added!
LikeLike